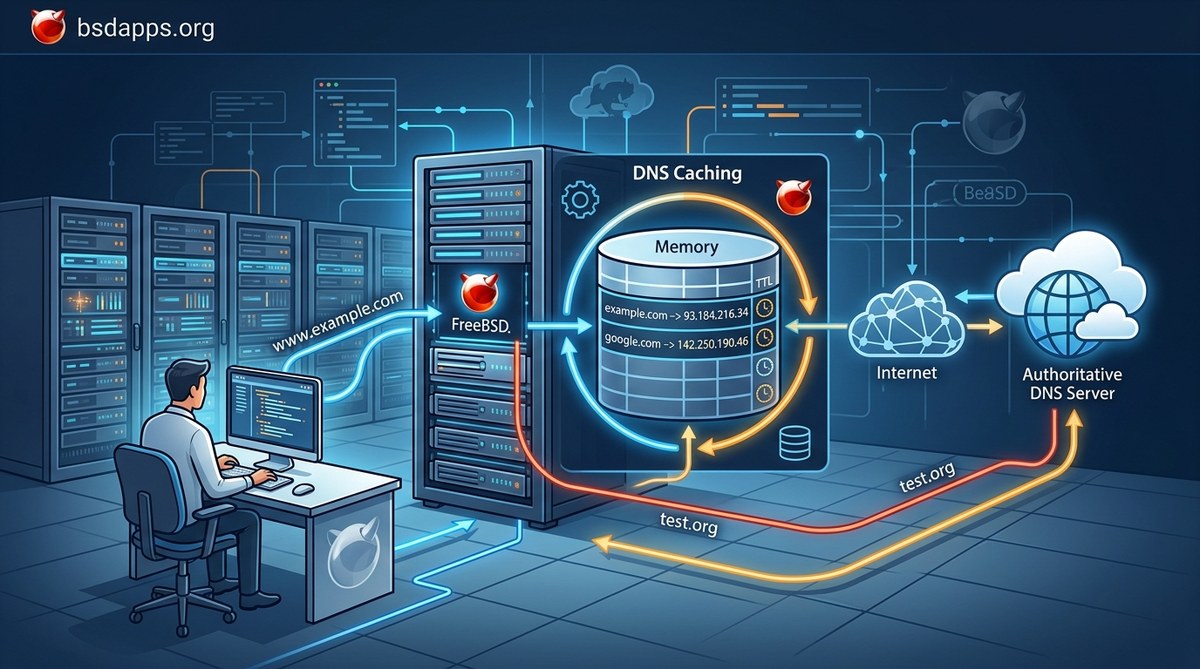
DNS caching may sound like a dry technical topic, but for BSD enthusiasts it is a practical tool that affects every login to a remote service, every software update, and every command you run that reaches the internet. If you have ever noticed a website loading faster after the first visit or you have run into an old DNS record resurfacing after you know it should be gone, you have seen caching in action. This guide is written for BSD users across OpenBSD, FreeBSD, and NetBSD. We will walk through what DNS cache is, why it matters to you, how it works across the BSD stack, and how you can manage caches safely and effectively on your system.
What is DNS caching and why BSD users care
DNS caching is a mechanism that stores results of previous DNS lookups so that future requests for the same domain name can be answered quickly without repeating the entire resolution process. Caches are distributed across multiple layers, and each layer has its own TTL that tells how long the cached data remains valid. For BSD users, caching matters because:
- It reduces latency and bandwidth usage by avoiding repeated queries to upstream DNS servers.
- It makes browsing feel snappier, especially on systems with limited network connectivity or when you are working with remote services.
- It can complicate testing and troubleshooting when stale data linger taxes the system.
- A well tuned BSD DNS stack balances performance and accuracy, especially when you enable DNSSEC and monitor NXDOMAIN behavior.
In the BSD world you will typically interact with a local resolver such as Unbound or a BIND instance, and you may also rely on browser caches and OS level caches. Understanding each layer helps you optimize the overall DNS experience without sacrificing correctness.
How DNS caching works
Types of DNS caches
- Browser cache
- Every modern browser caches DNS lookups to speed up page loading on repeated visits.
- Browser caching operates independently of the system and the network resolver.
- Operating system resolver cache
- BSD systems keep a cache of recent DNS answers in the resolver process itself.
- This cache speeds up DNS lookups made by applications that rely on the system resolver.
- Recursive resolver cache
- When your BSD machine queries a recursive resolver (for example your ISP or a public resolver), that resolver caches the answers too.
- The TTL in the DNS records controls how long that answer stays valid in the upstream cache.
- Negative caching
- If a domain does not exist or a record is temporarily unavailable, resolvers may cache that negative result for a period.
- This helps avoid repeated failed lookups, but it can also lead to persistent NXDOMAIN results if changes propagate slowly.
TTL matters
- Time to Live (TTL) is the duration a DNS answer is considered fresh.
- A longer TTL means faster responses but slower propagation of DNS changes.
- A shorter TTL improves responsiveness to changes but increases query load on the resolver and clients.
- TTL values can differ by record type (A, AAAA, CNAME, MX, etc.) and by zone configuration.
Positive vs negative caching
- Positive caching stores successful query results like an A record for example.com.
- Negative caching stores negative results such as NXDOMAIN, indicating a domain does not exist.
- Both types influence how quickly you see changes in domain availability and correctness.
DNS caching in the BSD world
Common BSD resolvers and caching behavior
- OpenBSD
- OpenBSD commonly uses Unbound as the local resolver.
- Unbound caches answers locally and can be configured for DNSSEC validation, access control, and performance tuning.
- FreeBSD
- FreeBSD users often run Unbound as the default local resolver, but BIND or dnsmasq can also be used.
- Unbound provides a robust caching layer, while BIND offers familiar enterprise grade features.
- NetBSD
- NetBSD supports Unbound with options to integrate other resolvers if needed.
- The preferred setup combines caching with security features like DNSSEC.
How to identify which resolver you are using
- Check if Unbound is installed and running
- Commands vary by OS and init system, but common indicators include a running unbound daemon and a socket or log entry.
- Check your resolver configuration
- Look at /etc/resolv.conf to see what nameserver lines are configured.
- Look for Unbound specific configuration files such as /var/unbound/unbound.conf or /etc/unbound/unbound.conf.
- Confirm the DNS lookup path
- Tools like dig or drill can help determine if your queries are resolved locally or by an upstream recursive resolver.
How to enable and configure DNS caching on BSD
- Unbound
- Install and enable Unbound as the local resolver.
- Typical configuration focuses on access control, DNSSEC || DNSSEC betrayal checks, and performance knobs like cache-max-ttl, cache-min-ttl, prefetch, and num-threads.
- Enabling prefetch can improve perceived performance for hot domains.
- dnsmasq or dnscrypt
- dnsmasq provides a lightweight caching resolver suited for small environments.
- dnscrypt (or dnscrypt-proxy) is useful for encryption and privacy alongside caching when used in conjunction with a local resolver.
- BIND
- BIND can be used as a local resolver on BSD but is more heavyweight; it provides extensive caching and zone management options.
Notes for BSD admins
– Always back up your resolver configuration before changing cache settings.
– When enabling DNSSEC, ensure your resolver validates DNSSEC records to protect against spoofing.
– Consider enabling access control lists to limit who can query the local resolver and reduce cache poaching.
Practical caching tips for BSD admins
- Use a fast, feature rich local resolver like Unbound to maximize caching benefits.
- Enable DNSSEC validation to mitigate DNS spoofing risks while still benefiting from caching.
- Tune the cache with parameters that fit your network profile, such as:
- cache-min-ttl
- cache-max-ttl
- num-threads
- prefetch during idle times
- Keep an eye on memory usage since large caches can consume substantial RAM on busy systems.
TTL, propagation, and caching behavior across networks
DNS propagation is a misconception. What propagates are the changes across caches along the path from authoritative servers to recursive resolvers to clients. TTLs govern how long each cached answer remains valid locally and in the recursive resolver chain.
- If you change an A record on the authoritative zone, the new value will not be visible to caches until their TTLs expire.
- Browsers may also have their own TTL logic separate from the OS resolver.
- In some cases, you may want to temporarily lower TTLs for records that are likely to change soon, to speed up propagation.
- In other scenarios, keeping TTLs longer reduces query load on your resolver and improves stability.
For BSD administrators that manage their own domains, understanding TTL is crucial when you roll out changes. Plan changes during maintenance windows if possible and reduce TTLs ahead of time so caches will flush more quickly when the change happens.
How to check and verify DNS caches on BSD
Checking caches is a mix of observing resolver state, testing behavior, and occasionally peeking at upstream cache behavior. Here are practical approaches for BSD users.
Quick checks with standard tools
- Use dig to test caching behavior
- First query a domain and note the returned TTL.
- Query the same domain again after a short interval and observe if the TTL appears refreshed or reduced.
- Example:
- dig example.org
- dig example.org
- If the second response has a lower TTL and similar data, you may be seeing the altered TTL due to the local cache.
- Use drill or host tools
- Tools like drill (from the ldns or ldnsutils package) offer additional output helpful for debugging DNS cache behavior.
- Inspect the resolver status
- If you are using Unbound, commands such as:
- unbound-control stats
- unbound-control dump_cache
- can give you current cache size and item counts. Availability depends on your Unbound version.
Cache inspection in the BSD ecosystem
- OpenBSD
- OpenBSD often runs Unbound via rcctl or an equivalent init framework.
- You can use doas or sudo with Unbound control utilities to inspect stats and cache contents.
- FreeBSD
- FreeBSD uses service or rcctl for managing Unbound. You can query the service status and request a cache review through Unbound control or by resting the service.
- NetBSD
- NetBSD follows similar patterns with rc.d scripts; you can inspect Unbound status and, if available, dump cache statistics.
Note about caches
– Local caches will show different results depending on whether domains were accessed via TLS/HTTPS, DNS over TLS, or other encrypted channels, as well as whether your apps bypass the resolver in favor of browser caches.
– Cache visibility is best measured with a combination of resolver stats and measured query results.
How to flush DNS caches on BSD
Flushing caches is sometimes necessary during troubleshooting, after a domain change, or when you suspect stale data is causing issues. The exact steps depend on the resolver you are using and the BSD flavor.
Unbound based caching
- Safe generic cache flush
- Command: sudo unbound-control flush
- This clears the internal cache across all cached entries.
- Alternative reboot based refresh
- Command: sudo service unbound restart
- Command: rcctl restart unbound
- Restarting the service also clears caches and reloads the configuration.
- OpenBSD specific notes
- OpenBSD users can perform the same unbound-control operations with elevated privileges or use rcctl to restart the daemon.
- FreeBSD specific notes
- FreeBSD users can run: sudo service unbound restart
- FreeBSD also supports rcctl restart unbound in newer setups.
- NetBSD specifics
- NetBSD: /etc/rc.d/unbound restart or rcctl restart unbound depending on your setup.
BIND caching
- If you use BIND locally
- Command: sudo rndc flush
- Command: sudo rndc reload
- Restart the named service if necessary: sudo service named restart
dnsmasq caching
- For dnsmasq setups
- Command: sudo service dnsmasq restart
- Command: sudo /etc/rc.d/dnsmasq restart
- Restarting dnsmasq clears its in memory cache and reloads its config.
Practical tips for BSD cache management
- When conducting a DNS change and you need it visible quickly, consider temporarily reducing TTL values on the authoritative zone a few days before the change. After the change propagates, you can revert TTL to your normal long values.
- After updating firewall or DNS security policies, a cache flush ensures no stale data is served.
- If you suspect cache poisoning or related security concerns, ensure your DNSSEC settings are enabled and validated.
Security considerations for DNS caching on BSD
- Cache poisoning risk
- Even with caching, your resolver should validate responses against DNSSEC if available to mitigate spoofing risks.
- Negative caching behavior
- NXDOMAIN caching should be considered when domains frequently appear and disappear; implement sensible TTL for negative responses to avoid long delays in reviving broken records.
- Private networks and caching
- In small offices or home labs, ensure that your local resolver is not exposing cached data unnecessarily and that access controls prevent unauthorized use.
Putting it all together for a BSD workflow
- Start with a reliable local resolver
- Unbound is a solid choice on most BSD systems due to its performance, security features, and ease of configuration.
- Tune TTLs with care
- For data that changes often, consider shorter TTLs during testing and longer TTLs in production to reduce unnecessary traffic.
- Monitor and test
- Regularly check resolver stats to ensure caches are performing well.
- Validate that DNSSEC is working and that cache behavior aligns with your expectations.
- Plan for testing and maintenance
- Prepare a plan for test changes requiring DNS updates. Use TTL deferral to minimize the time to propagate.
Final thoughts
DNS caching is not a single knob you twist once and forget. It is a layered system that touches the BSD stack from the kernel resolver through the user space applications and into upstream recursive resolvers. By understanding how caches operate at each level, BSD users can reduce latency, improve reliability, and maintain control over how and when DNS changes take effect. Remember to balance performance with correctness, leverage DNSSEC where possible, and keep your cache management procedures well documented in your system administration notes.
If you are building or refining a BSD DNS stack, this guide should serve as a practical reference. As you gain experience, you will know exactly when to flush caches, how to tune TTLs for your environment, and how to keep your DNS secure while delivering fast and accurate results to your users.








No Responses